- Manual Vpn Configuration For Mac Pro
- Itouch Vpn Configuration
- Vpn Unlimited Manual Configuration
- Manual Vpn Configuration For Mac Windows 10
- Manual Vpn Configuration For Mac Download
- Free Vpn For Mac
Set up a VPN connection on Mac. To connect to a virtual private network (VPN), you need to enter configuration settings in Network preferences. These settings include the VPN server address, account name, and any authentication settings, such as a password or a certificate you received from the network administrator. VPN client configuration files are contained in a zip file. Configuration files provide the settings required for a native Windows, Mac IKEv2 VPN, or Linux clients to connect to a VNet over Point-to-Site connections that use native Azure certificate authentication. Client configuration files are.
To connect to a virtual private network (VPN), you need to enter configuration settings in Network preferences. These settings include the VPN server address, account name, and any authentication settings, such as a password or a certificate you received from the network administrator.
If you received a VPN settings file from your network administrator, you can import it to set up your connection. If you didn’t, you can enter the settings manually.
Import a VPN settings file
On your Mac, do one of the following:
Double-click the file to open Network preferences and automatically import the settings.
Choose Apple menu > System Preferences, click Network, click the Action pop-up menu , then choose Import Configurations. Select the file, then click Import.
Enter VPN settings manually
On your Mac, choose Apple menu > System Preferences, then click Network.
Click the Add button in the list at the left, click the Interface pop-up menu, then choose VPN.
Click the VPN Type pop-up menu, then choose what kind of VPN connection you want to set up, depending on the network you are connecting to. Give the VPN service a name, then click Create.
L2TP is an extension of the Point-to-Point Tunneling Protocol used by Internet service providers to enable a VPN over the Internet.
IPSec (Internet Protocol Security) is a set of security protocols.
IKEv2 is a protocol that sets up a security association in IPSec.
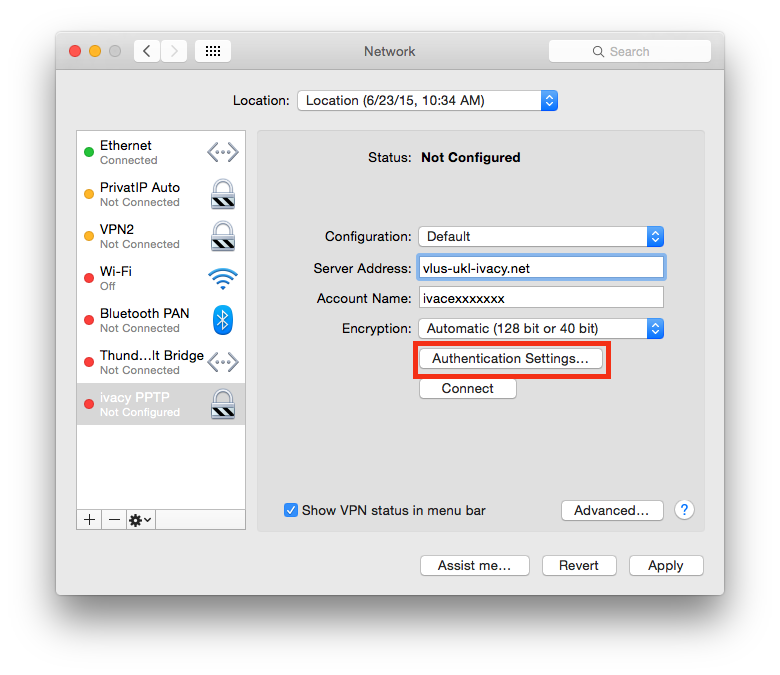
Enter the server address and the account name for the VPN connection.
Click Authentication Settings, then enter the information you received from the network administrator.
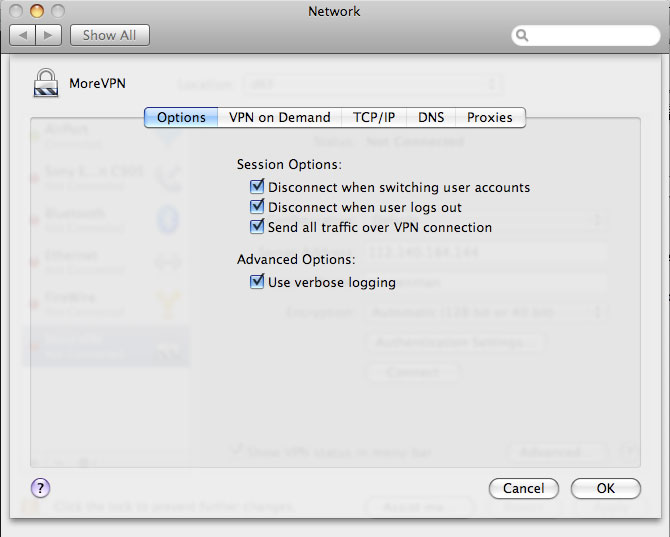
If specified by your network administrator, click Advanced to enter additional information such as session options, TCP/IP settings, DNS servers, and proxies.
The additional information you can enter depends on the type of VPN connection you’re setting up.
Click Apply, then click OK.
Select “Show VPN status in menu bar” to use the VPN status icon to connect to the network and switch between VPN services.
To remove the VPN configuration, select the VPN network connection service in the list and click the Remove button .
VPN client configuration files are contained in a zip file. Configuration files provide the settings required for a native Windows, Mac IKEv2 VPN, or Linux clients to connect to a VNet over Point-to-Site connections that use native Azure certificate authentication.
Client configuration files are specific to the VPN configuration for the VNet. If there are any changes to the Point-to-Site VPN configuration after you generate the VPN client configuration files, such as the VPN protocol type or authentication type, be sure to generate new VPN client configuration files for your user devices.
- For more information about Point-to-Site connections, see About Point-to-Site VPN.
- For OpenVPN instructions, see Configure OpenVPN for P2S and Configure OpenVPN clients.
Important
Starting July 1, 2018, support is being removed for TLS 1.0 and 1.1 from Azure VPN Gateway. VPN Gateway will support only TLS 1.2. Only point-to-site connections are impacted; site-to-site connections will not be affected. If you’re using TLS for point-to-site VPNs on Windows 10 clients, you don’t need to take any action. If you are using TLS for point-to-site connections on Windows 7 and Windows 8 clients, see the VPN Gateway FAQ for update instructions.
Generate VPN client configuration files
Before you begin, make sure that all connecting users have a valid certificate installed on the user's device. For more information about installing a client certificate, see Install a client certificate.
You can generate client configuration files using PowerShell, or by using the Azure portal. Either method returns the same zip file. Unzip the file to view the following folders:
- WindowsAmd64 and WindowsX86, which contain the Windows 32-bit and 64-bit installer packages, respectively. The WindowsAmd64 installer package is for all supported 64-bit Windows clients, not just Amd.
- Generic, which contains general information used to create your own VPN client configuration. The Generic folder is provided if IKEv2 or SSTP+IKEv2 was configured on the gateway. If only SSTP is configured, then the Generic folder is not present.
Generate files using the Azure portal
- In the Azure portal, navigate to the virtual network gateway for the virtual network that you want to connect to.
- On the virtual network gateway page, click Point-to-site configuration.
- At the top of the Point-to-site configuration page, click Download VPN client. It takes a few minutes for the client configuration package to generate.
- Your browser indicates that a client configuration zip file is available. It is named the same name as your gateway. Unzip the file to view the folders.
Generate files using PowerShell
Note
This article has been updated to use the new Azure PowerShell Azmodule. You can still use the AzureRM module, which will continue to receive bug fixes until at least December 2020.To learn more about the new Az module and AzureRM compatibility, seeIntroducing the new Azure PowerShell Az module. ForAz module installation instructions, see Install Azure PowerShell.
When generating VPN client configuration files, the value for '-AuthenticationMethod' is 'EapTls'. Generate the VPN client configuration files using the following command:
Copy the URL to your browser to download the zip file, then unzip the file to view the folders.
Windows
You can use the same VPN client configuration package on each Windows client computer, as long as the version matches the architecture for the client. For the list of client operating systems that are supported, see the Point-to-Site section of the VPN Gateway FAQ.
Note
You must have Administrator rights on the Windows client computer from which you want to connect.
Use the following steps to configure the native Windows VPN client for certificate authentication:
- Select the VPN client configuration files that correspond to the architecture of the Windows computer. For a 64-bit processor architecture, choose the 'VpnClientSetupAmd64' installer package. For a 32-bit processor architecture, choose the 'VpnClientSetupX86' installer package.
- Double-click the package to install it. If you see a SmartScreen popup, click More info, then Run anyway.
- On the client computer, navigate to Network Settings and click VPN. The VPN connection shows the name of the virtual network that it connects to.
- Before you attempt to connect, verify that you have installed a client certificate on the client computer. A client certificate is required for authentication when using the native Azure certificate authentication type. For more information about generating certificates, see Generate Certificates. For information about how to install a client certificate, see Install a client certificate.
Mac (OS X)
You have to manually configure the native IKEv2 VPN client on every Mac that will connect to Azure. Azure does not provide mobileconfig file for native Azure certificate authentication. The Generic contains all of the information that you need for configuration. If you don't see the Generic folder in your download, it's likely that IKEv2 was not selected as a tunnel type. Note that the VPN gateway Basic SKU does not support IKEv2. Once IKEv2 is selected, generate the zip file again to retrieve the Generic folder.
The Generic folder contains the following files:
- VpnSettings.xml, which contains important settings like server address and tunnel type.
- VpnServerRoot.cer, which contains the root certificate required to validate the Azure VPN Gateway during P2S connection setup.
Use the following steps to configure the native VPN client on Mac for certificate authentication. You have to complete these steps on every Mac that will connect to Azure:
Import the VpnServerRoot root certificate to your Mac. This can be done by copying the file over to your Mac and double-clicking on it. Click Add to import.
Note
Double-clicking on the certificate may not display the Add dialog, but the certificate is installed in the correct store. You can check for the certificate in the login keychain under the certificates category.
Verify that you have installed a client certificate that was issued by the root certificate that you uploaded to Azure when you configured you P2S settings. This is different from the VPNServerRoot that you installed in the previous step. The client certificate is used for authentication and is required. For more information about generating certificates, see Generate Certificates. For information about how to install a client certificate, see Install a client certificate.
Open the Network dialog under Network Preferences and click '+' to create a new VPN client connection profile for a P2S connection to the Azure VNet.
The Interface value is 'VPN' and VPN Type value is 'IKEv2'. Specify a name for the profile in the Service Name field, then click Create to create the VPN client connection profile.
In the Generic folder, from the VpnSettings.xml file, copy the VpnServer tag value. Paste this value in the Server Address and Remote ID fields of the profile.
Click Authentication Settings and select Certificate.
Click Select… to choose the client certificate that you want to use for authentication. This is the certificate that you installed in Step 2.
Choose An Identity displays a list of certificates for you to choose from. Select the proper certificate, then click Continue.
In the Local ID field, specify the name of the certificate (from Step 6). In this example, it is 'ikev2Client.com'. Then, click Apply button to save the changes.
On the Network dialog, click Apply to save all changes. Then, click Connect to start the P2S connection to the Azure VNet.
Linux (strongSwan GUI)
Install strongSwan
The following configuration was used for the steps below:
| Computer | Ubuntu Server 18.04 |
| Dependencies | strongSwan |
Use the following commands to install the required strongSwan configuration:
Use the following command to install the Azure command-line interface:
Generate certificates
If you have not already generated certificates, use the following steps:
Manual Vpn Configuration For Mac Pro
Generate the CA certificate.
Print the CA certificate in base64 format. This is the format that is supported by Azure. You will later upload this to Azure as part of your P2S configuration.
Generate the user certificate.
Generate a p12 bundle containing the user certificate. This bundle will be used in the next steps when working with the client configuration files.
Install and configure
Itouch Vpn Configuration
The following instructions were created on Ubuntu 18.0.4. Ubuntu 16.0.10 does not support strongSwan GUI. If you want to use Ubuntu 16.0.10, you will have to use the command line. The examples below may not match screens that you see, depending on your version of Linux and strongSwan.
Open the Terminal to install strongSwan and its Network Manager by running the command in the example.
Select Settings , then select Network.
Click the + button to create a new connection.
Select IPsec/IKEv2 (strongSwan) from the menu, and double-click. You can name your connection in this step.
Open the VpnSettings.xml file from the Generic folder contained in the downloaded client configuration files. Find the tag called VpnServer and copy the name, beginning with 'azuregateway' and ending with '.cloudapp.net'.
Paste this name into the Address field of your new VPN connection in the Gateway section. Next, select the folder icon at the end of the Certificate field, browse to the Generic folder, and select the VpnServerRoot file.
In the Client section of the connection, for Authentication, select Certificate/private key. For Certificate and Private key, choose the certificate and the private key that were created earlier. In Options, select Request an inner IP address. Then, click Add.
Turn the connection On.
Linux (strongSwan CLI)
Install strongSwan
Vpn Unlimited Manual Configuration
The following configuration was used for the steps below:
| Computer | Ubuntu Server 18.04 |
| Dependencies | strongSwan |
Use the following commands to install the required strongSwan configuration:
Use the following command to install the Azure command-line interface:
Generate certificates
If you have not already generated certificates, use the following steps:
Generate the CA certificate.
Print the CA certificate in base64 format. This is the format that is supported by Azure. You will later upload this to Azure as part of your P2S configuration.
Generate the user certificate.
Generate a p12 bundle containing the user certificate. This bundle will be used in the next steps when working with the client configuration files.
Install and configure
Manual Vpn Configuration For Mac Windows 10
Download the VPNClient package from Azure portal.
Extract the File.
From the Generic folder, copy or move the VpnServerRoot.cer to /etc/ipsec.d/cacerts.
Copy or move cp client.p12 to /etc/ipsec.d/private/. This file is client certificate for Azure VPN Gateway.
Open VpnSettings.xml file and copy the
<VpnServer>value. You will use this value in the next step.Adjust the values in the example below, then add the example to the /etc/ipsec.conf configuration.
Add the following to /etc/ipsec.secrets.
Run the following commands:
Manual Vpn Configuration For Mac Download
Next steps
Return to the article to complete your P2S configuration.
Free Vpn For Mac
To troubleshoot P2S connections, see the following articles: